Lifetouch, Shutterfly, and Epstein: What’s Verified, What’s Not, and Why Parents Want Transparency
This Unsealed Report examines questions surrounding Lifetouch, Shutterfly, Apollo Global Management, and the documented financial relationship between Jeffrey Epstein and Leon Black. The report explores why parents have raised concerns about child-related data, school photography systems, and corporate ownership structures while emphasizing that there is no public evidence linking Epstein to Lifetouch operations or student information. By analyzing Epstein’s history of exploiting access, influence, and trusted institutions, the investigation examines broader issues of transparency, child safety, data security, and the safeguards parents should expect from companies and vendors that work with schools and minors.
Let’s be clear from the start: Jeffrey Epstein was a documented predator who targeted minors. He did not “accidentally” end up around children. He built a world where access, silence, and protection were easier to buy than accountability.
This post is not here to protect his reputation. It’s here to protect our awareness.
When people hear “school photography,” they don’t think “risk.” They think picture day, class photos, and order forms sent home in backpacks. It feels harmless. Familiar. Routine.
And that’s exactly why it matters to talk about it through the lens of Epstein’s life and patterns — because Epstein thrived in systems that looked normal from the outside.
Why parents are asking about Lifetouch
Lifetouch is one of the most common school photography companies in the U.S. Millions of children are photographed. Images are processed, stored, and delivered through modern systems that families rarely see.
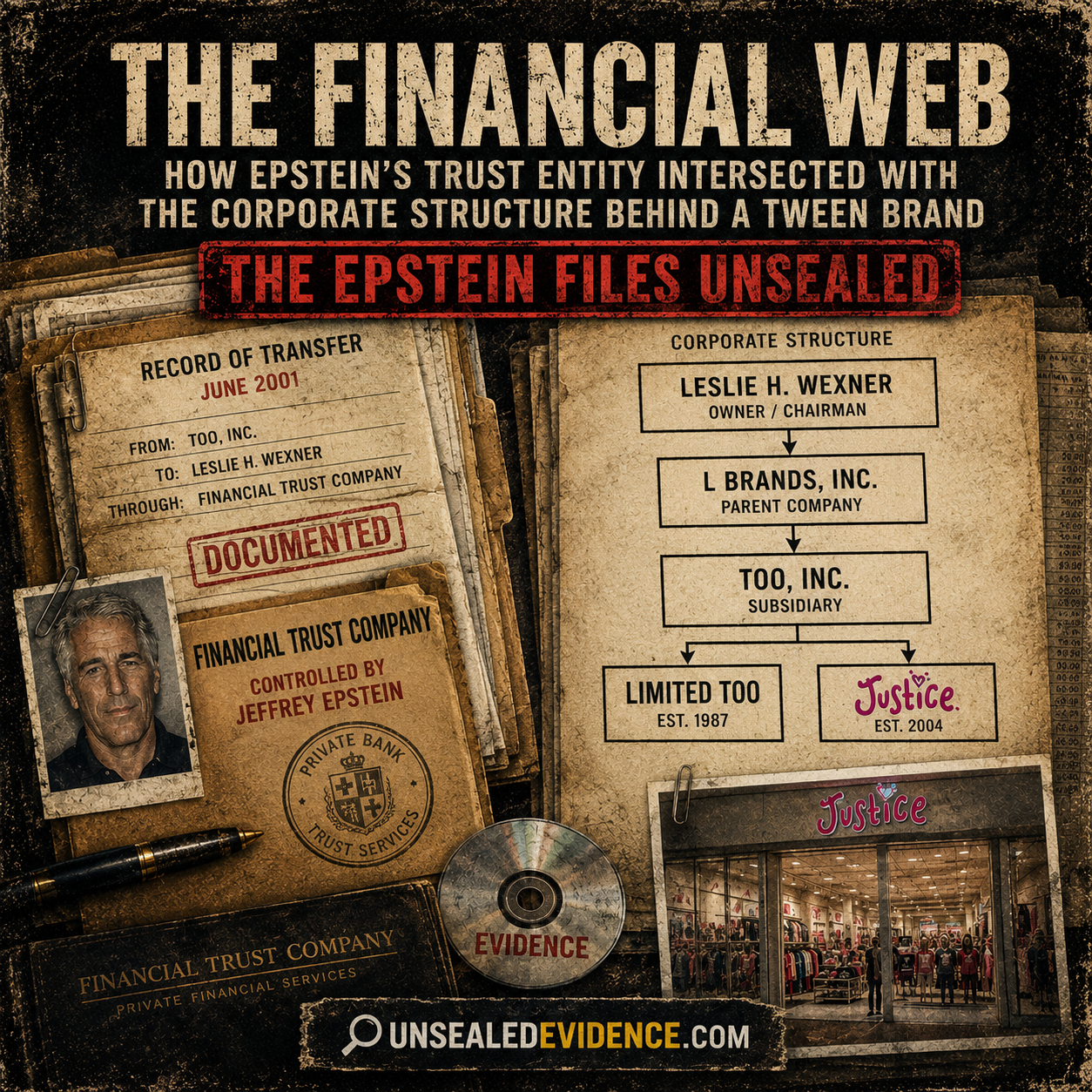
Lifetouch is owned by Shutterfly. Shutterfly was acquired by Apollo Global Management. Apollo was co-founded by Leon Black.
Leon Black has a publicly documented financial relationship with Jeffrey Epstein. Black paid Epstein very large sums of money over time. Black has described those payments as professional services, but the scale of that relationship is what makes people stop and ask questions.
Parents aren’t wrong to feel uneasy when:
- a school-facing company is part of a much larger corporate chain, and
- that chain leads to powerful figures with documented ties to Epstein.
The question IS “Did Epstein have access?” — and we have to handle that honestly
Yes. One of the questions parents are asking is: Did Epstein ever gain access to school photo data or child-related information through corporate networks?
Right now, there is no public proof that Epstein accessed Lifetouch systems, obtained student data, or had any direct connection to Lifetouch operations. There is also no released document showing Lifetouch data being provided to Epstein.
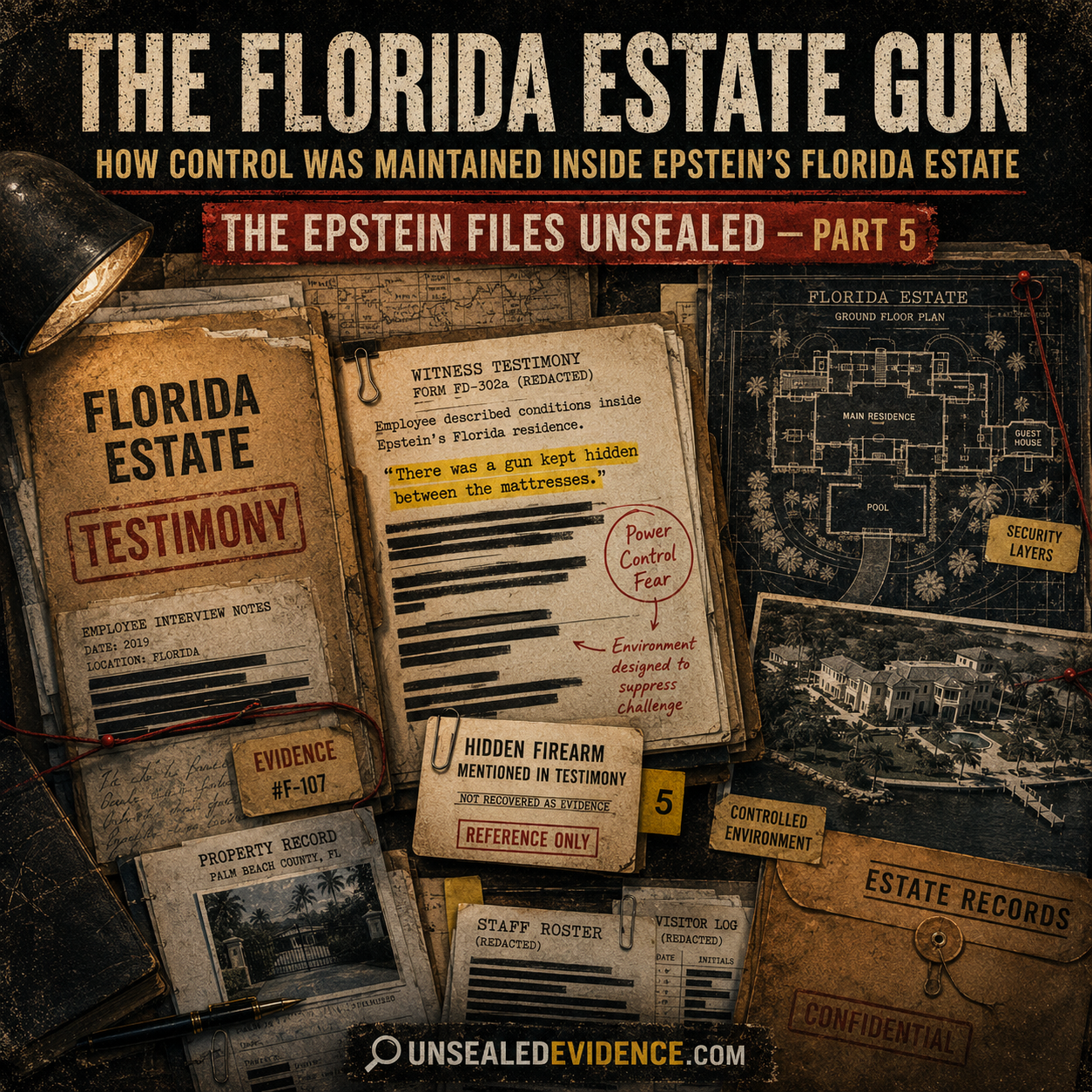
But here is the uncomfortable truth that makes this worth discussing anyway: Epstein’s money and connections created opportunities that ordinary people cannot see.
That is not an accusation toward Lifetouch. It is an observation about Epstein — a man who repeatedly used wealth and influence to gain access to people, places, and protection that should never have been available to him.
Why predators seek systems involving children
This is hard to talk about, but it’s important — and it’s exactly why parents are asking questions in the first place.
Predators don’t usually show up wearing a label that says “danger.” They seek out environments where access looks normal, where their presence won’t raise alarms, and where adults assume that someone else has done the vetting.
Systems involving children can be attractive to predators because they often include:
- predictable schedules (events, calendars, school routines)
- trusted access points (vendors, volunteers, “official” roles)
- lots of personal information (names, photos, grade levels, sometimes more)
- institutional blind spots (contractors and third parties that aren’t scrutinized like employees)
- social cover (“I’m here for work,” “I’m approved,” “I’m with the company”)
That does not mean every system is unsafe. It means the system must be built to be safe — with transparency, strict limits, and accountability.
Epstein’s history matters here because it shows what happens when powerful people are treated as exceptions, when concerns are brushed off, and when “it’s probably fine” becomes the default.
Why “no proof” isn’t the same as “no risk”
We have to be responsible with language. We cannot claim something happened without evidence. But we also can’t ignore how Epstein operated just because we don’t have a document spelling out every single “how.”
Epstein’s story is full of gaps where:
- people looked away,
- institutions assumed “someone else vetted him,” and
- powerful connections kept doors open that should have slammed shut.
So when parents ask, “Could a predator like Epstein pay for access to information?” that question is not irrational. It’s informed by how he lived.
And when a documented predator has financial ties to billionaires, it is fair to ask what protections exist — not because we’re claiming a specific breach happened, but because Epstein’s entire history is a lesson in what becomes possible when money meets weak oversight.
What parents should focus on (actionable, not fear-based)
This is the part that matters most: whether the company is Lifetouch or any other vendor, parents deserve transparency about child-related data and images.
If your child’s school uses a photography vendor, here are reasonable questions to ask the school or district:
- What student information is provided to the vendor? (Name, grade, teacher, student ID, etc.)
- Is any sensitive data included? (Birthdates, addresses, contact details — and if yes, why?)
- Where are student photos stored? (Cloud provider, internal servers, third parties)
- Who can access the system? (Vendor staff, subcontractors, school staff)
- How long are photos stored? What is the retention policy?
- Can a parent request deletion? If yes, how?
- What security standards are contractually required?
Epstein didn’t succeed because people asked too many questions. He succeeded because people didn’t ask enough.
The point of this post
Lifetouch is not being accused here.
The point is Epstein — and what his money, influence, and high-level relationships demonstrate: predators don’t always look like predators, and they don’t operate alone.
Even when we can’t prove a specific act in a specific system, Epstein’s history should change how we think about child safety in the real world. Not panic. Not paranoia. Preparedness.
Because the lesson of Epstein is simple and brutal: creeps are not rare, and access is not accidental.